If you have taken measures against DoS or DDoS attacks and you would like to know whether those work efficiently, then it is recommended you carry out a DDoS test.
What is a DDoS test?
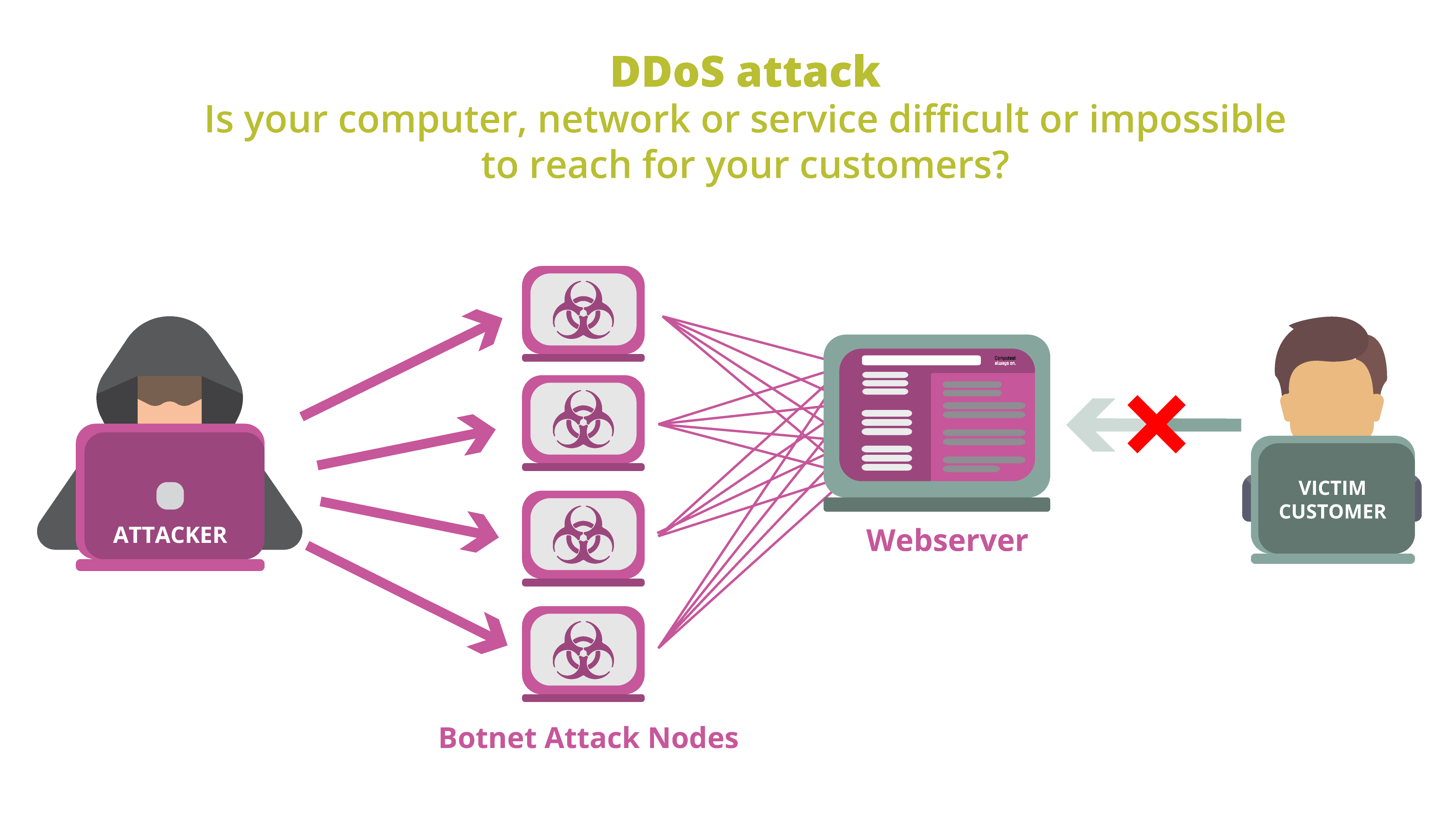
The aim of a (D)DoS attack is usually to disrupt a network or service and to make that unfit for use. Often in the case of DDoS attacks a network of systems/computers is used for that purpose. The larger the network, the greater the difficulty is in guarding against such an attack. DoS attacks are smaller and easier to ward off, but by using the right software they can easily be carried out from almost every computer. A DDoS test will make it clear to what extent your application is protected against attacks. By simulating a DoS or DDoS attack in a controlled situation, you can gain clarity as to whether your protection measures hold up.
What do we do during a DDoS test?
During a DDoS test we carry out an attack in a controlled situation, while simulating a group of users in your application. In this way you can find out how vulnerable your security is and what the impact of the attack could be on your infrastructure and the users’ experience as the scale of the attack increases. Instead of a botnet, we use our own infrastructure (supplemented with cloud infrastructure) in order to simulate various attacks in a controlled manner. We slowly increase the intensity so that it clearly becomes visible from which moment and which place users will experience problems from the attack. Moreover, we repeat certain series of steps, which allows administrators to find out what they should be watching out for and how they can best react.
Our DDoS test simulates the most frequently occurring types of attacks, such as:
- SYN Flood
- UDP Flood
- DNS amplification attack
- Connection Flood
- Request Flood
- Slowloris attack
What do you get after a DDoS test?
You will be provided with a report on the basis of the DDoS test. The report will contain the test results, which we will personally go through with you extensively. You will also be provided with aids in order to strengthen your defence against DDoS attacks.
